You understand the problem. You’ve tried to solve it with existing tools. You’re suffering or your manager is asking if there is a better way. The good news is that there is.Documentation Index
Fetch the complete documentation index at: https://docs.provisionr.io/llms.txt
Use this file to discover all available pages before exploring further.
TL;DR
The root cause of most access requests is that organizations don’t have a way to define and enforce policies for who should belong to which groups and resources based on rich user attribute metadata. We are relying on humans to manually decide if access is appropriate, when our systems should be able to make those decisions automatically based on policy. Unfortunately, the authorization automation and the administrator experience for advanced policy management got neglected. Most SSO and identity providers offer only basic string-matching group rules that break as organizational complexity increases. They consider their group rules to be “feature complete”. Those rules are just the tip of the iceberg. Our customers outgrewthis equals that a long time ago, and have been putting in band-aids ever since.
String-Matching Rules
String-matching group rules in Google Workspace and Okta work well at first—until organizational complexity outgrows them. As companies scale and user attributes evolve, teams spend more time maintaining brittle rules than benefiting from the automation. Consider how often departments or teams get renamed, merged, or split in a typical year. Consider how many variations of “Sales Account Executive” exist across regions because different managers use different naming conventions. Each change breaks existing string-matching rules and requires manual cleanup.We explore why string matching breaks down in IdP Group Rule Sprawl, examine a real-world case study in Why Sales Teams Break Access Automation, and trace how simple rules become unmaintainable in The Hidden Complexity of Group Membership Rules.
Infrastructure-as-Code (IaC) and GitOps
Configuration-as-code approaches using Ansible, Terraform, or JSON/YAML flat files provide state management through Git repositories. These approaches work well for infrastructure, but they hit limits when applied to identity management at scale—especially when trying to offer self-service. It’s unrealistic to expect non-engineering users to open merge requests for their access needs. Flat file databases can’t handle relationships. Moving configuration state to a Git repository doesn’t eliminate the busy work — it just relocates it.Google Administration Manager (GAM)
GAM is a powerful command-line tool for managing Google Workspace. It reduces click-ops in the admin console, but it still requires building and maintaining custom scripts for group membership management. The manual process remains underneath the automation layer. GAM users will feel at home with the Provisionr CLI.Complex No-Code Workflows
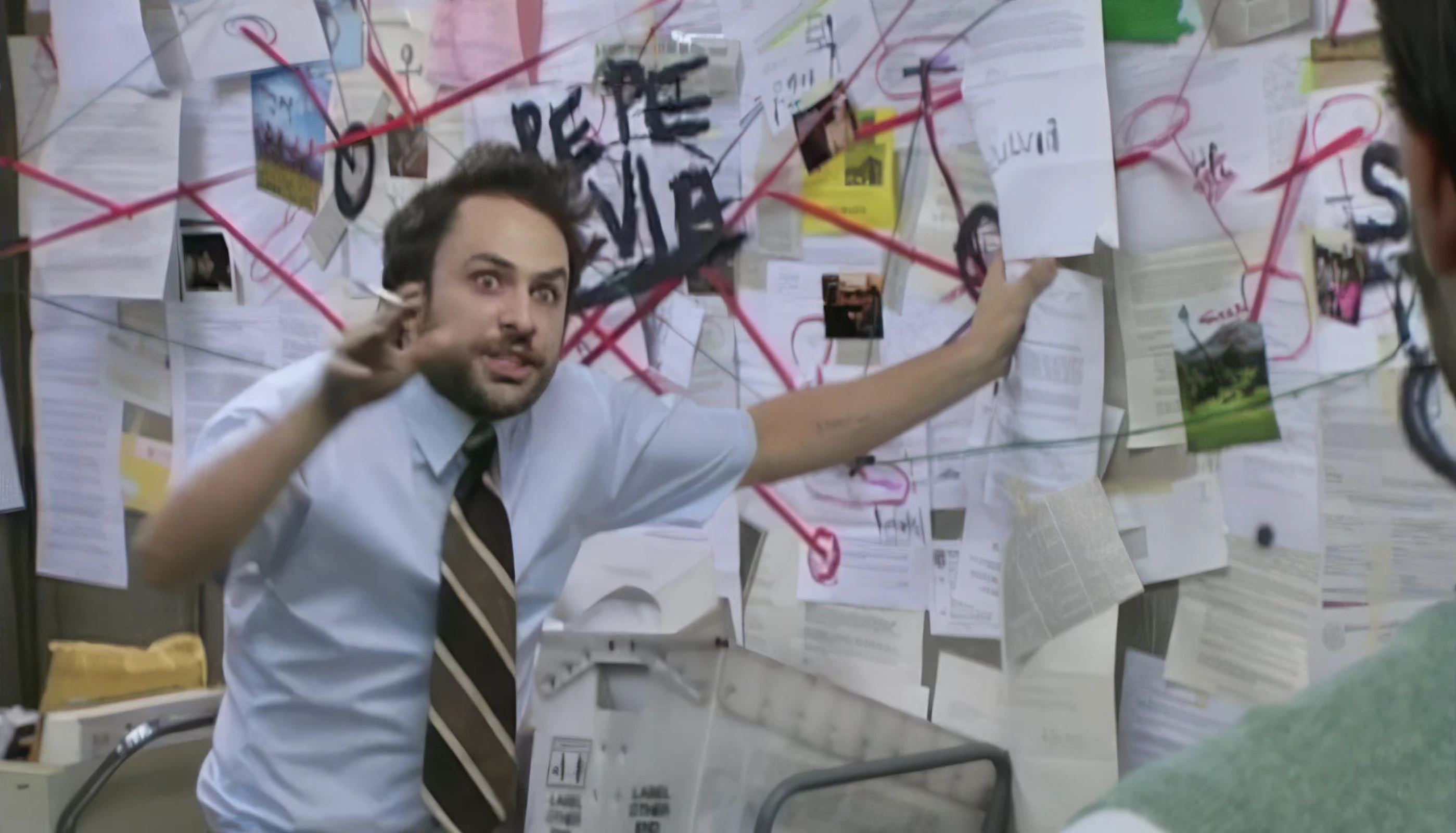
No-code platforms like n8n, Okta Workflows, Tines, Zapier, etc promise automation without programming. For identity provisioning, that promise falls apart quickly. A workflow that should be simple—determine if a user belongs in a group—becomes a 20-30 step maze of conditional logic. Fetch user data from an API. Parse the JSON response. Handle errors when the API times out. Grab a value from a nested array. Use that value to call another API. Repeat for three other systems. String concatenate fields together to see if they match a group name. Add a row to an exception Google Sheet when the group name isn’t found. Each step requires configuration. Each step can fail. Most platforms lack real data transformation capabilities, so you’re left chaining together workarounds. Need to normalize a job title before matching? That’s another five steps. Need to handle null values? More branching logic. The result is a visual flowchart that rivals any spaghetti code. When your string-matching logic breaks—and it will—debugging a 30-step workflow is no easier than debugging a script. Worse, the logic is scattered across UI panels instead of being readable in a single file. Use your no-code platform for what it does best — simple automations and integrations based on webhook events. If this happens, then do that. It’s not a comprehensive extract-transform-load (ETL) engine or a rules engine, and it doesn’t have it’s own database for cached or calculated data. No-code workflows become their own version of homegrown scripts—just harder to version control, harder to test, and harder to hand off to the next person.Python Scripts
The pattern is familiar to anyone who has worked in IT operations. Python scripts read from HRIS systems or CSV exports, generate group membership changes, and run in CI/CD pipelines. Over time, edge cases accumulate and the scripts become harder to maintain. Audit trails are incomplete or nonexistent. Self-service for non-engineering users remains impractical. Each new system that needs group membership management requires yet another script. How many hours a month do you spend poking at these scripts to keep them running? How many edge cases have you had to build in over time? Can your team easily audit who made what changes and why? What happens when you need to onboard a new system that needs group membership management—do you have to build more scripts? What about approval policies? Can you handle pre-approval logic so that just-in-time access is pre-approved? Scripts only get you so far, and they introduce more risk than most teams realize. A relational database with generated IDs provides capabilities that JSON flat files in CI/CD pipelines simply cannot match at scale. But does the organization have staff to invent and maintain a custom solution? Companies with 10,000+ employees might. If you have fewer than that, probably not. And if you do have the staff, are they spending their time on this or on strategic initiatives that help your organization grow securely?We break down the build vs. buy decision with real numbers in Building vs. Buying Access Management Infrastructure, explain the integration challenges in The Integration Layer, and quantify the hidden costs in The Cost of Manual Provisioning.